CBS’ CIO: Cyber security is like a cold war

(GIF: GentlemanScholar/Giphy)
Increasing threat levels for cybercrime and espionage against universities have resulted in a pamphlet on preventing “foreign interference” published by the Danish Security and Intelligence Service (PET) and the ministry. CBS’ CIO explains the innate dilemma between how universities operate and cyber security, and that we all need to be a little more skeptical and watchful.
On December 23, 2019, University of Maastricht’s critical systems for business operations, including mail servers and file servers full of research data, as well as backup servers were attacked.
The attack was orchestrated by Russian hackers, who, since October, had gained access to the university’s systems and IT infrastructure via phishing mails. And after gaining access, they installed so-called ransomware, which they launched on December 23. The ransomware made it possible for the hackers to both steal and encrypt the university’s data.
The Russian hackers then asked the university to pay a ransom worth 30 Bitcoins, at the time worth 200,000 euros or DKK 1.5 million, to unblock its computer systems. In the end, the University of Maastricht paid the ransom.
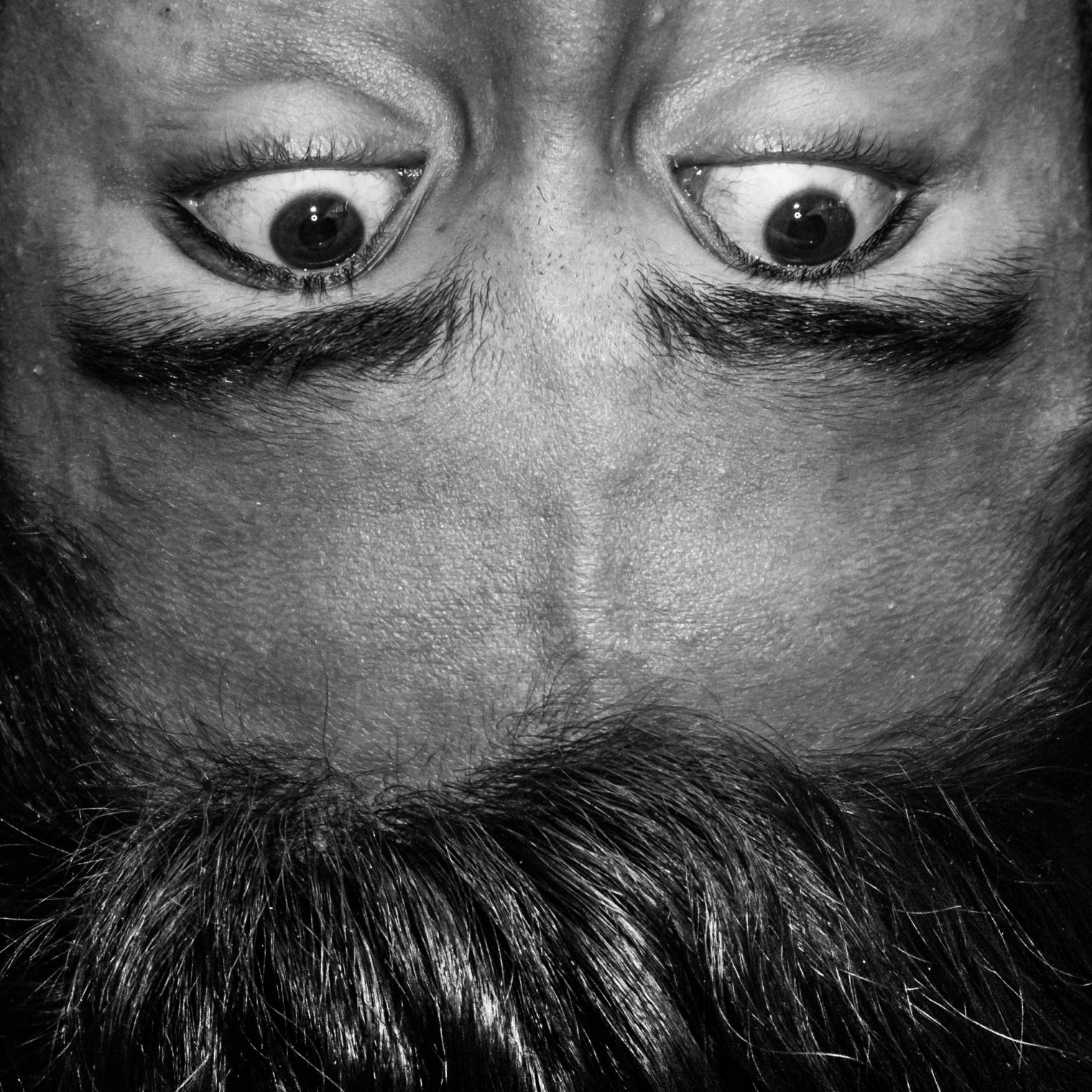
“This is the bogey, and exactly what we are trying to protect ourselves against,” says Niels Jespersen, CIO at CBS.
For Niels Jespersen, cyber security is a theme ever present in his work, however, it has gained some extra airtime, as the Danish Security and Intelligence Service (PET) along with the Ministry of Higher Education and Science have published the pamphlet ‘Is your research at risk?’ with tips on foreign interference and espionage for researchers and other staff.
The pamphlet describes various cases of espionage and cybercrime. For example, how Aalborg University cooperated with a PhD student who published research papers in collaboration with an engineer from the Zhengzhou Institute of Information Science and Technology, which they later found out does not exist. Instead, it is used as a cover for the Chinese military university PLA Information Engineering University, which specializes in signal intelligence and development of defense technology.
“The Chinese PhD student obtained knowledge about sophisticated signal technology that may optimize wireless signals in 5G mobile networks and satellite and radar systems” the pamphlet states.
The universities are built on a paradigm of complete openness and dialogue, whereas cyber security is based on a large degree of not sharing too much
Niels Jespersen
Espionage is just one of three areas where universities are experiencing a high threat level, explains Niels Jespersen. The second threat is the so-called insider threat, which describes the risk of staff or students intentionally – but mostly without knowing – exposing or sharing data with unauthorized persons.
But the biggest threat is like the one from ransomware.
“The threat from ransomware has developed and overtaken the other two areas. If you ignore that it’s a crime, this kind of crime is very professional and user friendly. The criminals have support systems the victims can call for help and guidance. I have not seen the websites from where they operate, but they have been described to me,” he says and continues:
“It was also a ransomware attack that shut off the Colonial Pipeline on the East Coast of the US. So it is a major threat.”
The innate dilemma
According to the meeting material for the CBS Board meeting held on April 12, CBS had 32 “critical incidents” concerning cyber security in 2020. Of the 32 incidents, 29 of them were related to human errors. The remaining three incidents were categorized as serious, and included two hacks on a blog server that was not properly updated. The two hacks on the blog server resulted in several CBS websites being offline for days – including CBS WIRE.
To avoid future incidents like those in 2020, CBS has introduced multifactor authentication for a number of CBS systems as well as abolishing permanent access to administration rights on PCs, according to the meeting material.
However, cyber security in the university sector is special.
Knowledge sharing and openness is a prerequisite for researchers and employees, but as Niels Jespersen points out, this is the root cause of an innate dilemma.
“The universities are built on a paradigm of complete openness and dialogue, whereas cyber security is based on a large degree of not sharing too much. This is an obvious conflict, and our job is to balance the two. When I talk to cyber security professionals who do not work in the university sector, they say it’s a lost cause to even have unknown software on your computer. I don’t believe so,” he says.
Niels Jespersen explains that the issue of cyber security is like a cold war.
“Whenever we get a new means of protection, the attacks develop. And that’s why attacks with ransomware have become worse. Originally, they only had the capacity to encrypt data. You could then refuse to pay the ransom and just restore the data from your backup. But now they steal the data beforehand and threat to publish personal data, and that’s a step up,” he says and continues:
“Moreover, just a couple of years ago, the attacks were directed at individuals, now entire corporations and organizations are in their sights.”
Security like an onion
When the University of Maastricht was attacked, it ended up paying the ransom after considering the alternatives, which would have included rebuilding its entire IT network from scratch, according to Reuters.com.
But if you ask Niels Jespersen, paying the ransom should never be a solution.
“Don’t pay the ransom. Period. When I hear about corporations or organizations that pay the ransom, I get frustrated, because it’s not a solution, it just makes it lucrative to continue the enterprise,” he says and continues:
“I know that you can be in a situation where the risk of not paying the ransom far exceeds the risk of paying it. And since it’s such a big issue, we can hope that the different countries’ cyber security units are working on tracking down the criminal masterminds behind the attacks, although it’s tough to find them.”
As cybercrime is a field in continuous development, Niels Jespersen does not believe that it is possible to hedge one’s bets. However, based on the principle of an onion, multiple layers of security should give the virtual intruders a harder time.
“The best prevention we have is actually to teach ourselves and our colleagues to behave as safely as possible. We have a lot of technical features, but experience shows that if individual employees and students are on their toes, that is when we gain the best prevention,” he says.
For example, CBS regularly sends out fake phishing mails to employees, and based on how many open the emails and click on the links, it is possible to increase awareness and direct information to people who click on phishing emails.
“For us, it is very important that we don’t shame people for clicking the links in the phishing emails – whether they be fake or not. What’s important is that it’s possible to restore whatever damage it has caused. And we spend a lot of time explaining that. When we run the tests with the fake phishing mails still too many people react to them, so we need to keep discussing how to bring down the figures,” he says.
Moreover, CBS is currently recruiting a person for the cyber security team at CBS’ IT Department.
But overall, Niels Jespersen asks employees as well as students to just be skeptical.
“Of course, we have a technical setup that spares us for most problems, but you get the biggest security on an individual level. We all need to be a little more skeptical and watchful. The moment you have the slightest doubt about something, contact IT Support then we can help clarifying whether something is up,” he says.































































































































HI Manu,
It’s a guy called GentlemanScholar. You can check it out here: https://giphy.com/gifs/gentlemanscholar-gentlemanscholar-upwork-equifax-security-xT8pe2M9qM4bidp4GY
Who did this amazing illustrated animation ?